The BitLocker encryption will help to keep your volume or the flash drive in a safe mode. But if you do not need the BitLocker encryption any more, you can remove the BitLocker encryption easily on Windows 10 computer. Here, we will show you the four ways to remove/disable BitLocker drive encryption on Windows 10.
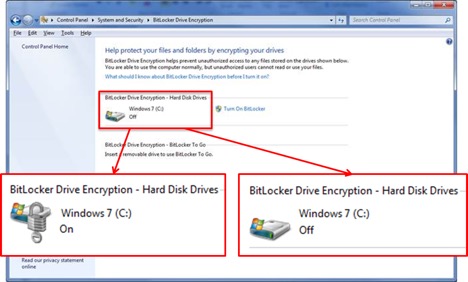
Open, Read & Write a BitLocker Drive in Mac. The next and last but not least step is to open the BitLocker drive on Mac. Now connect the BitLocker encrypted drive to the Mac and open the software you had installed for opening the BitLocker encrypted drive. Once it’s opened, right click on the drive and select Mount Drive which means open drive. It is the perfect cross-platform solution for people who work both on Windows and Mac OS. It is an ideal tool to read BitLocker encrypted drives on Mac. I can read/write the BitLocker drive on Mac as if it is the native drive. 5-star quality and service. To access a BitLocker drive on Mac OS X, you have to firstly connect the drive to a Windows computer and then simply go to Control Panel System and Security BitLocker Drive Encryption to turn off BitLocker encryption on this drive. If you cannot find any Windows machine, you have to use a third-party utility to access the BitLocker drive on.
Video guide on how to remove BitLocker drive encryption on Windows 10 desktop:
Way 1: Remove BitLocker Encryption through Control Panel
Step 1: Click Computer and go to open Control Panel. Among the computer’ setting, you need to select the System and Security.
Step 2: Choose BitLocker Drive Encryption to Manage BitLocker. In the BitLocker Drive Encryption interface, tap Turn off BitLocker and re-confirm your option. In this way, your drive is no longer in BitLocker password protection.

Way 2: Disable BitLocker Encryption with BitLocker Manager
Before you access BitLocker Manager, you should unlock the BitLocker encrypted drive with the password or recovery key.
Step 1: Hold Windows key and press E.
Step 2: Choose This PC and then you will see the Devices and the Drives. Choose your BitLocker drive and right-click on the mouse. As a result, you will get the Manage BitLocker Option.
Step 3:Enter the BitLocker Drive Encryption interface, you are offered a series of options. To disable the BitLocker encryption, you need to click Turn off BitLocker. After that, you will get a notice about this action, click Turn off BitLocker again. In the end, the BitLocker encryption will not work on your drive.
Way 3: Disable BitLocker through Windows PowerShell.
Step 1: Search powershell in the Windows Start Search and select the Windows PowerShell program.
Step 2: When you open Windows PowerShell as the administrator, you can type Disable-Bitlocker –MountPoint “drive letter:” in it, just as the screenshot shows.
Step 3:Press Enter and the BitLocker drive decryption process will begin. In a short time, your BitLocker protection will be turned off for the drive.
Way 4: Turn off BitLocker with Command Prompt.
Step 1: Press Windows + X, select Command Prompt (Admin) to run command prompt as an administrator.
Step 2: Type the following command as the screenshot shows: manage-bde -unlock F: -RecoveryPassword YOUR-BITLOCKER-RECOVERY-KEY .
Step 3: Launch manage-bde -off f: to remove BitLocker drive encryption.
External Tips: How to Unlock BitLocker USB on Mac

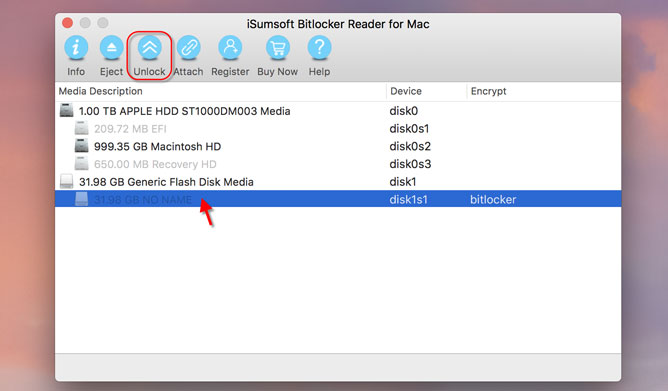
In common situation, when we put the USB with BitLocker-encryption into Mac computer, it will pop out the window that tells us the USB is unreadable. But with BitLocker Genius, you can open, read and access the BitLocker encrypted USB in 4 steps:
- 1. Run the software and make the USB connected with the Mac.
- 2. Select the BitLocker USB and click the Unlock button on the navigation bar.
- 3. Enter the password of the USB and click the Mount button.
- 4. The decrypted USB is displayed on the desktop successfully.
Related Articles:
-->Use Intune to configure BitLocker Drive Encryption on devices that run Windows 10.
BitLocker is available on devices that run Windows 10 or later. Some settings for BitLocker require the device have a supported TPM.
Use one of the following policy types to configure BitLocker on your managed devices
Endpoint security disk encryption policy for Windows 10 BitLocker. The BitLocker profile in Endpoint security is a focused group of settings that is dedicated to configuring BitLocker.
View the BitLocker settings that are available in BitLocker profiles from disk encryption policy.
Device configuration profile for endpoint protection for Windows 10 BitLocker. BitLocker settings are one of the available settings categories for Windows 10 endpoint protection.
View the BitLocker settings that are available for BitLocker in endpoint protection profiles form device configuration policy.
Tip
Intune provides a built-in encryption report that presents details about the encryption status of devices, across all your managed devices. After Intune encrypts a Windows 10 device with BitLocker, you can view and retrieve BitLocker recovery keys when you view the encryption report.
You can also access important information for BitLocker from your devices, as found in Azure Active Directory (Azure AD).encryption report that presents details about the encryption status of devices, across all your managed devices.
Permissions to manage BitLocker
To manage BitLocker in Intune, your account must have the applicable Intune role-based access control (RBAC) permissions.
Following are the BitLocker permissions, which are part of the Remote tasks category, and the built-in RBAC roles that grant the permission:
Bitlocker For Mac Users
- Rotate BitLocker Keys
- Help Desk Operator
Create and deploy policy
Use one of the following procedures to create the policy type you prefer.
Create an endpoint security policy for BitLocker
Sign in to the Microsoft Endpoint Manager admin center.
Select Endpoint security > Disk encryption > Create Policy.
Set the following options:
- Platform: Windows 10 or later
- Profile: BitLocker
On the Configuration settings page, configure settings for BitLocker to meet your business needs.
If you want to enable BitLocker silently, see Silently enable BitLocker on devices, in this article for additional prerequisites and the specific setting configurations you must use.
Select Next.
On the Scope (Tags) page, choose Select scope tags to open the Select tags pane to assign scope tags to the profile.
Select Next to continue.
On the Assignments page, select the groups that will receive this profile. For more information on assigning profiles, see Assign user and device profiles.
Select Next.
On the Review + create page, when you're done, choose Create. The new profile is displayed in the list when you select the policy type for the profile you created.
Create a device configuration profile for BitLocker
Sign in to the Microsoft Endpoint Manager admin center.
Select Devices > Configuration profiles > Create profile.
Set the following options:
- Platform: Windows 10 and later
- Profile type: Endpoint protection
Select Settings > Windows Encryption.
Configure settings for BitLocker to meet your business needs.
If you want to enable BitLocker silently, see Silently enable BitLocker on devices, in this article for additional prerequisites and the specific setting configurations you must use.
Select OK.
Complete configuration of additional settings, and then save the profile.
Manage BitLocker
To view information about devices that receive BitLocker policy, see Monitor disk encryption. You can also view and retrieve BitLocker recovery keys when you view the encryption report.
Silently enable BitLocker on devices
You can configure a BitLocker policy that automatically and silently enables BitLocker on a device. That means that BitLocker enables successfully without presenting any UI to the end user, even when that user isn't a local Administrator on the device.
Device Prerequisites:
A device must meet the following conditions to be eligible for silently enabling BitLocker:
- If end users log in to the devices as Administrators, the device must run Windows 10 version 1803 or later.
- If end users log in to the the devices as Standard Users, the device must run Windows 10 version 1809 or later.
- The device must be Azure AD Joined
- Device must contain TPM (Trusted Platform Module) 2.0
- The BIOS mode must be set to Native UEFI only.
BitLocker policy configuration:
The following two settings for BitLocker base settings must be configured in the BitLocker policy:
- Warning for other disk encryption = Block.
- Allow standard users to enable encryption during Azure AD Join = Allow
The BitLocker policy must not require use of a startup PIN or startup key. When a TPM startup PIN or startup key is required, BitLocker can't silently enable and requires interaction from the end user. This requirement is met through the following three BitLocker OS drive settings in the same policy:
- Compatible TPM startup PIN must not be set to Require startup PIN with TPM
- Compatible TPM startup key must not set to Require startup key with TPM
- Compatible TPM startup key and PIN must not set to Require startup key and PIN with TPM
View details for recovery keys
Intune provides access to the Azure AD blade for BitLocker so you can view BitLocker Key IDs and recovery keys for your Windows 10 devices, from within the Intune portal. To be accessible, the device must have its keys escrowed to Azure AD.
Bitlocker For Mac Free
Sign in to the Microsoft Endpoint Manager admin center.
Select Devices > All devices.
Select a device from the list, and then under Monitor, select Recovery keys.
Hit Show Recovery Key. Selecting this will generate an audit log entry under 'KeyManagement' activity.
When keys are available in Azure AD, the following information is available:
- BitLocker Key ID
- BitLocker Recovery Key
- Drive Type
When keys aren't in Azure AD, Intune will display No BitLocker key found for this device.
Information for BitLocker is obtained using the BitLocker configuration service provider (CSP). BitLocker CSP is supported on Windows 10 version 1703 and later, and for Windows 10 Pro version 1809 and later.
For more information on Audit Log entries, see Azure Portal audit logs.
Rotate BitLocker recovery keys
You can use an Intune device action to remotely rotate the BitLocker recovery key of a device that runs Windows 10 version 1909 or later.
Prerequisites
Devices must meet the following prerequisites to support rotation of the BitLocker recovery key:
Devices must run Windows 10 version 1909 or later
Azure AD-joined and Hybrid-joined devices must have support for key rotation enabled via BitLocker policy configuration:
- Client-driven recovery password rotation to Enable rotation on Azure AD-joined devices or Enable rotation on Azure AD and Hybrid-joined devices
- Save BitLocker recovery information to Azure Active Directory to Enabled
- Store recovery information in Azure Active Directory before enabling BitLocker to Required
To rotate the BitLocker recovery key
Sign in to the Microsoft Endpoint Manager admin center.
Select Devices > All devices.
In the list of devices that you manage, select a device, select More, and then select the BitLocker key rotation device remote action.
On the Overview page of the device, select the BitLocker key rotation. If you don’t see this option, select the ellipsis (…) to show additional options, and then select the BitLocker key rotation device remote action.
Bitlocker Download Mac